List Categories and Listings by T
Halon is an email software distribution. It provides a full stack, scriptable approach to functions such as delivery (SMTP/LMTP), routing, security (anti-spam, signing), automation and integration; everything you need in front of your email storage. You ...
SecureTrack empowers large corporations to automate and streamline Firewall management activities. With Tufin SecureTrack, you can effectively audit your Firewall, monitor policy changes in real-time and test changes for compliance with corporate policies ...
The @stake Sleuth Kit (TASK) allows an investigator examine the file systems of a suspect computer in a non-intrusive fashion. TASK is a collection of UNIX-based command line tools that can analyze NTFS, FAT, FFS, EXT2FS, and EXT3FS file systems. TASK rea ...
ThreatSim attack simulation product provides a phishing-focused security awareness training program. The ThreatSim mock attack system allows you to deliver simulated phishing emails with embedded Teachable Moments, which display targeted "just-in-time tea ...
Lightspeed Systems' content filtering, as part of Total Traffic Control (TTC), provides the most complete and cost-effective solution on the market. With TTC's content filter, you can: * Monitor and report all network traffic * Own a huge content fil ...
The objective of this program is to gather emails, subdomains, hosts, employee names, open ports and banners from different public sources like search engines, PGP key servers and SHODAN computer database. This tool is intended to help Penetration tester ...
The weakest link in most systems is invariably the human element. How do you ensure that confidential files do not get uploaded to the cloud?, how can you tell if a disgruntled employee is carrying out malicious activities which compromise the integrity o ...
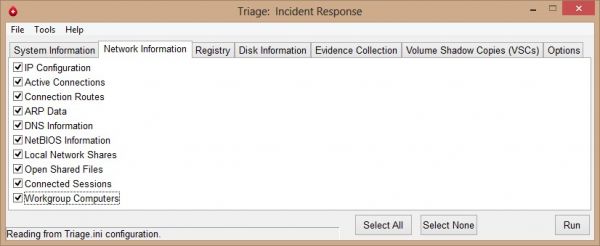
Triage-IR is a script written by Michael Ahrendt, which will collect system information, network information, registry hives, disk information and will also dump memory. One of the capabilities of Triage-IR is collecting information from Volume Shadow Cop ...
Tcpflow is a program that captures data transmitted as part of TCP connections (flows), and stores the data in a way that is convenient for protocol analysis and debugging. Each TCP flow is stored in its own file. Thus, the typical TCP flow will be stored ...
Trellix Email Security – Server leads the industry in identifying, isolating, and immediately stopping URL and attachment-based attacks, before they enter an organization’s environment. Email Security - Server provides real-time detection and preve ...
SecPoint delivers online vulnerability scanning service. You get the following benefits: Online Vulnerability Scanning Get HTML, XML, PDF Reports Get Clear Solutions how to fix the found vulnerabilities User Friendly interface Scan any operating ...
Deep Security protects confidential data and critical applications to help prevent data breaches and ensure business continuity, while enabling compliance with important standards and regulations such as PCI, FISMA and HIPAA. Whether implemented as softwa ...
Discover and protect sensitive data on premises and in the cloud. Identify Business Critical DataClassify structured and unstructured data with exact data matching and over 300 content types. Get Powerful ReportingCreate reports on demand or schedule fo ...
TEF is a fully-featured, secure and has advanced capabilities including the intuitive Xsentry easy-to-use administration graphical user interface with WYSIWYG (What You See Is What You Get) front end which has drag and drop security policy deployment.
Trend Micro Internet Security provides smart, up-to-date protection for your home network against present and future threats without slowing down your PC. Surf the web without worry Smart security features in Trend Micro Internet Security protect the comp ...
Trustwave MailMarshal is a sophisticated multi-layered approach to email security to reduce false positives and protect against spam, gateway attacks, viruses, phishing attempts, and malicious URLs embedded in email. It provides complete email protection ...
Total Defense Essential Anti-Virus Internet Security Malware protection – simple, smart, and reliable protection from viruses, spyware, ransomware and other malware threats on up to 3 of your PCsMulti-layer technology – real-time and on-demand malware sc ...
Trustway Globull is a highly-secure external drive that allows users to address mobility issues and respond to the need for high levels of security — up to defense-level security.
Tripwire Enterprise is the configuration control solution that combines best-of-breed file integrity monitoring with comprehensive compliance policy management to protect, detect and correct IT systems throughout the modern enterprise. As a part of the Tr ...
Traffic Sentinel makes use of embedded instrumentation within switches, routers, load balancers, and servers. Industry standard sFlow provides the richest information, greatest scalability, and is supported by the largest number of vendors (see sFlow Capa ...