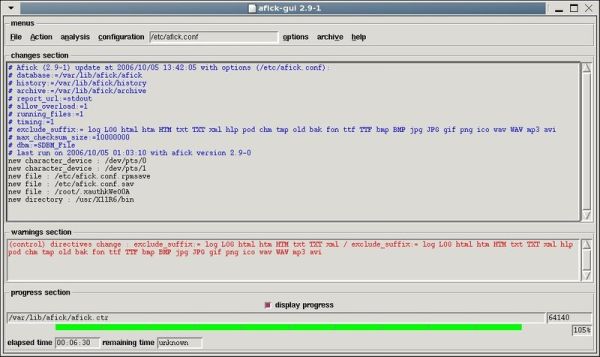
AFICK
Afick is a security tool, very close from to well known tripwire. It allows to monitor the changes on your file systems, and so can detect intrusions.
It's designed to be quick and portable. For now, it has been tested on
- Windows XP, 2000, Vista, Seven, 10 with ActiveState's ActivePerl
- linux Redhat (7.1, 7.3)
- linux Fedora core (6 to 33)
- linux Mandrake/Mandriva (8.2 to 2011.0)
- linux Mageia (2 to 7 )
- linux Suse Enterprise server 8.0, OpenSuse 11.x
- linux Debian (3 to 10, Knoopix)
- linux Ubuntu (6.04 to 20.10)
- linux Slackware (9.1)
- HP Tru64 Unix 5.1B
- HPUX 11
- AIX 5.2.0
but it should work on any computer with perl and its standard modules.
Rating
0 vote
Favoured:
0
Listing Details
Vendor
Eric Gerbier
Website
Pricing Model
Open Source
Modified
Never
Owner
Created