DeviceLock DLP Suite
DeviceLock DLP Suite consists of five modules that protect your organization from data leak threats:
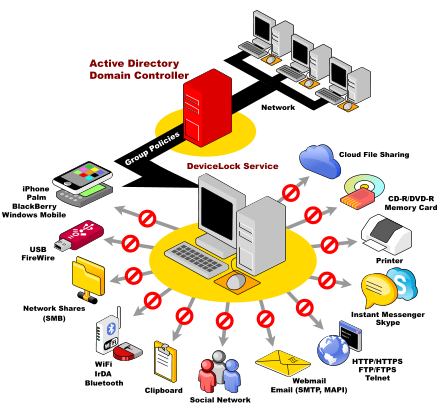
- DeviceLock provides network administrators the ability to set and enforce contextual policies for how, when, where to, and by whom data can or can’t be moved to or from company laptops or desktop PCs via devices like phones, digital cameras, USB sticks, CD/DVD-R, tablets, printers or MP3 players. In addition, policies can be set and enforced for copy operations via the Windows Clipboard, as well as screenshot operations on the endpoint computer.
- NetworkLock adds contextual-level control of user network communications via the Internet through such means as: company email, personal webmail, instant messaging services, social networks (like Facebook, Google+, Twitter), web surfing, FTP file transfers, as well as cloud-based file sharing services like Dropbox, SkyDrive and Google Drive.
- ContentLock adds the capability to look inside files and other data objects (like emails and webmails, chats, blog posts, etc.) for sensitive information like social security numbers, credit card numbers, bank account numbers or other user-definable information and to make block-or-allow decisions based on policies having to do with file contents.
- Discovery is a separately licensed component, which helps network administrators and security personnel locating certain types of content stored within and outside the limits of the corporate network. Discovering unwanted content is essential when trying to protect the company’s intellectual property, control employee activities and administer computer networks.
- Search Server is an optional separately licensed component, which provides full-text searching of logged data. The full-text search functionality is especially useful in situations when you need to search for shadow copies of documents based on their contents.
The combination of all of these modules working together is the DeviceLock DLP Suite. The DLP Suite provides protection against local and network data leaks at the endpoint (laptop, desktop or server) via a wide array of threat vectors.
Rating
0 vote
Favoured:
0
Listing Details
Vendor
DeviceLock, Inc.
Website
Pricing Model
Commercial
Modified
Owner
Created