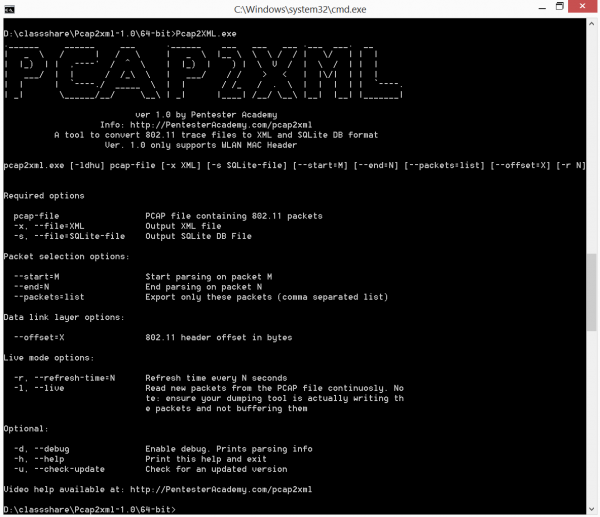
PCAP2XML
PCAP2XML is a tool suite which takes 802.11 PCAP trace files as input and can convert them into XML or SQLITE representations. This allows a pentester to run arbitrary queries on the packet header fields.
Why do we need this?
Wireshark is great when it comes to capturing and filtering packet traces. However, it has no facility for macro level tasks. Here are some answers which Wireshark cannot give you out of the box:
- Give me all device MAC addresses in the PCAP
- Give me a unique list of all Access Point/Ad-Hoc networks in the PCAP
Of course, this is by design. Wireshark is a packet capture tool and not a data analysis platform.
This is where Pcap2XMl/Sqlite comes in! We map every header field in an 802.11 packet to an XML and SQLITE Equivalent. Once we convert every packet into these formats, it is extremely easy to run analysis tools on them as you shall see in latter part of this post.
Where can this tool be used?This tool can be used anywhere there is a need to analyze individual packets. However, we had the following purposes in mind:
- Teaching Wi-Fi security using Packet Analysis
- Deriving Macro-Stats on a PCAP file as discussed in the previous section
- Writing a simple Wi-Fi IDS